May 12th, 2015 by Elma Jane

Our company’s goal is to make our customer happy. Our Merchant is very important with us. At National Transaction it’s all about our customer service. Yet many customers would rather than not contact a company for support, and this is especially true in the tech world. Customer finds the support experience as frustrating and time-wasting exercise.
We know this is true because we are customers ourselves. We’ve all felt that palpable sense of dread when we have to call a toll-free support number, expecting a massive, circular phone tree followed by a seemingly endless wait, and possibly a clueless rep when (if!) we finally do reach a human being.
It doesn’t have to be that way, at National Transaction we manage customer support delivery because we know we have an obligation to make it work. NTC’s teamwork-focused strategy and effective application of technology and data, can help our customer service do their jobs better.
How it works:
Apply lessons learned to continuously improve service – Some issues customers raise are a one-off, but many times, patterns emerge that can deliver insights on how the company could improve service for everyone.
It can be difficult for a single agent or manager to identify patterns, which is why a customer support platform with robust reporting capabilities is crucial to enable continuous service improvement.
In a crowded marketplace, excellence in customer support can be a key differentiator for a business. When customers reach out for support, they’re usually already stressed out about something that’s not working as expected. Far too often, their stress level increases while they’re attempting to get help, due to poorly designed business processes.
If your customers are stressed out, you can change that by taking a new approach. Make sure you know who they are when they reach out, and allow them to contact you on their own terms. Access your company’s collective expertise to quickly resolve the customer’s problems.
Be honest with the customer – A good customer support agent really does want to make things right for the customer, and that’s admirable. However, it’s important to avoid making commitments you can’t keep, which will serve only to increase the customer’s dissatisfaction in the long run.
Always be honest with your customers. If you can’t solve their problem immediately, give them an accurate time frame for a resolution, and let them know what steps you’re taking to address the issue. Record the commitment on a customer database so colleagues are up-to-date on your activities.
Be honest about what you can and cannot do, and take a look at the big picture, so you can improve service not only for the customer on the line but for everyone else.
Give customers multiple channels to access help – Customers have unique needs and individual preferences, Give them choices.
Know who your customers are – There are few among us who haven’t experienced the frustration of a poorly designed phone tree and the indignity of being shuffled from agent to agent and asked for our name, account number, product type and current service issue over and over again. Stop doing that to your customers.
Deploy a technology platform that incorporates a customer database with product and inventory information. That way, you’ll know who your customers are and what products they use when they call, and if you have to transfer them to another agent for help, the next agent will have that information too.
Use teamwork to solve customer issues – Chances are, someone in your company is capable of solving any problem a customer brings to the support team, but that person might not be on the phone. That’s why collaboration is so important.
There are software solutions that make collaborating across business units simple, and enable agents to view notes about past customer issues for clues to solving current problems. This not only helps your company solve the problem at hand, but also allows you to manage the entire relationship.
By following these steps, you can reduce your customers’ stress level and your own.
Posted in Best Practices for Merchants, nationaltransaction.com Tagged with: account, customer service, customer support, data, database, merchant, software, transaction
January 23rd, 2015 by Elma Jane
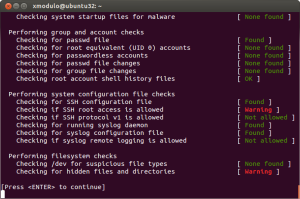
Technology and software are among the most important investments a company can make, especially when it comes to security. Growing demand for IT services and security solutions prove that business owners know the threats that are out there and want to do something to guard themselves against cybercriminals.
With a well-rounded security solution a business might purchased, and with all the recommended features a business might need, was the investment really worth it? Security solutions provider Trustwave, found that organizations of all sizes are wasting their security dollars and none more so than small businesses.
Small businesses spent an average of $157 per user on security software, compared with $73 per user in larger companies. Nearly 30 percent of that investment ended up underutilized or never used due to non- or misuse of security controls and features. And yet, companies still increased their spending by 44 percent.
Why did businesses end up letting their security software go partially to waste, despite significant increases in IT spending?
Many organizations cited a lack of resources: Either IT staff was too busy to implement their security solutions properly, or didn’t have the manpower to do so.
With the alarming number of high-profile corporate breaches, businesses of all sizes are aware that they need to invest in top-of-the-line solutions. IT professionals expect a 43 percent increase in their use of cloud-based or managed security services. But the financial constraints many small companies face can prove to be an obstacle to proper security.
A few IT-related tips to help save money, which can then be reallocated toward the technological and staffing resources needed to protect a business.
Monitor software usage and eliminate solutions that aren’t being used. Seek out products that are designed for small business. Some companies offer free or discounted versions of their product to very small companies. Track any IT/software purchases to ensure you’re within your budget.
Posted in Best Practices for Merchants Tagged with: breaches, Security, security software, services, software, solutions provider, technology
September 17th, 2014 by Elma Jane
Host Card Emulation (HCE) offers virtual payment card issuers the promise of removing dependencies on secure element issuers such as mobile network operators (MNOs). HCE allows issuers to run the payment application in the operating system (OS) environment of the smart phone, so the issuing bank does not depend on a secure element issuer. This means lower barriers to entry and potentially a boost to the NFC ecosystem in general. The issuer will have to deal with the absence of a hardware secure element, since the OS environment itself cannot offer equivalent security. The issuer must mitigate risk using software based techniques, to reduce the risk of an attack. Considering that the risk is based on probability of an attack times the impact of an attack, mitigation measures will generally be geared towards minimizing either one of those.
To reduce the probability of an attack, various software based methods are available. The most obvious one in this category is to move part of the hardware secure element’s functionality from the device to the cloud (thus creating a cloud based secure element). This effectively means that valuable assets are not stored in the easily accessible device, but in the cloud. Secondly, user and hardware verification methods can be implemented. The mobile application itself can be secured with software based technologies.
Should an attack occur, several approaches exist for mitigating the Impact of such an attack. On an application level, it is straightforward to impose transaction constraints (allowing low value and/or a limited number of transactions per timeframe, geographical limitations). But the most characteristic risk mitigation method associated with HCE is to devaluate the assets that are contained by the mobile app, that is to tokenize such assets. Tokenization is based on replacing valuable assets with something that has no value to an attacker, and for which the relation to the valuable asset is established only in the cloud. Since the token itself has no value to the attacker it may be stored in the mobile app. The principle of tokenization is leveraged in the cloud based payments specifications which are (or will soon be) issued by the different card schemes such as Visa and MasterCard.
HCE gives the issuer complete autonomy in defining and implementing the payment application and required risk mitigations (of course within the boundaries set by the schemes). However, the hardware based security approach allowed for a strict separation between the issuance of the mobile payment application on one hand and the transactions performed with that application on the other hand. For the technology and operations related to the issuance, a bank had the option of outsourcing it to a third party (a Trusted Service Manager). From the payment transaction processing perspective, there would be negligible impact and it would practically be business as usual for the bank.
This is quite different for HCE-based approaches. As a consequence of tokenization, the issuance and transaction domains become entangled. The platform involved in generating the tokens, which constitute payment credentials and are therefore related to the issuance domain, is also involved in the transaction authorization.
HCE is offering autonomy to the banks because it brings independence of secure element issuers. But this comes at a cost, namely the full insourcing of all related technologies and systems. Outsourcing becomes less of an option, largely due to the entanglement of the issuance and transaction validation processes, as a result of tokenization.
Posted in Best Practices for Merchants, Credit Card Security, EMV EuroPay MasterCard Visa, Near Field Communication, Visa MasterCard American Express Tagged with: (MNOs), (OS), assets, bank, card, card issuers, cloud, cloud based payments, cloud based secure element, cloud-based, hardware secure element, Host Card Emulation (HCE), issuing bank, MasterCard, mobile, mobile app, mobile application, mobile network operators, mobile payment, mobile payment application, nfc, operating system, payment application, payment transaction, payments, platform, risk, secure element, smart phone, software, software based technologies, token, tokenization, transaction, virtual payment, visa
September 12th, 2014 by Elma Jane
Over the last couple of years, Big Data has become a huge buzzword in the business world. Whether this data comes from social networks, purchase histories, Web browsing patterns or surveys.
The vast amount of consumer information that brands can gather and analyze has allowed them to improve and personalize their customers’ experiences. But for all the attention Big Data has received, many companies tend to forget about one application of it…Employee Engagement.
When done in the right way, tracking, analyzing and sharing employee performance metrics can be very beneficial for both you and your staff. One of the things that is very powerful is being able to analyze real-time information, boil it down into performance data and empower employees with reports from that data. If you can provide employees with data to do their job better in a succinct, actionable way, it’s very motivating.
The more Big Data can be incorporated into an intimate individual experience, the better. This demonstrates to the employee that the experience is not just off the shelf and that it is relevant to the person. This personal relevance is shown to deliver higher engagement.
Applying Big Data analytics to employees’ performance helps identify and acknowledge not only the top performers, but the struggling or unhappy workers as well.
If you want to introduce analytics technology to your employee engagement strategies, below are a few tips to help you.
Find a program that integrates with your current systems. For any new software that you implement within your company, it’s important to make the transition as seamless and simple for your employees as possible.
The software has to work where the employees work already. You can’t make them switch tasks and go to another platform to aggregate the data stream. The software should genuinely assist the end user. Your choice of software should be a grassroots decision, and you should have buy-in from your employees before you ask them to use the new system.
Consider how employees will view themselves and others. Once you introduce performance and engagement analytics into your company, you’ll have to consider how that program fits into employee relationships and workplace culture as a whole.
A company needs to take into consideration the actions of the employee’s co-workers and how to make these data points of interest to the employee. This helps to foster a respected and trusting engagement experience and data needs to be used to build trust. No matter what solution you choose, an analytics program moves you away from the traditional manual reporting process of performance measurement; helping make your staff more efficient, motivated and engaged.
Business software is in the beginning stages of being useful for performance measurement. Businesses have not pushed for innovation as hard as consumers have, but now that’s starting to change. Think about business processes in a different way and gather data in a way that matters.
Select and focus on the most important metrics.Analytics programs can pull and process data for a large number of metrics. Even when applying Big Data to customer service, many businesses struggle to keep up with the volume of information pouring in. Narrowing down your focus to only the most important key performance indicators (KPIs). Don’t introduce too many metrics, it becomes too difficult and confusing. If you can boil it down to some very simple statistics, like a score that incorporates the elements you want, everyone can focus on consolidated KPIs.
Posted in Best Practices for Merchants Tagged with: big data, Business software, consumer, customer, customer service, data, key performance indicators, program, service, social networks, software, web, Web browsing patterns
September 10th, 2014 by Elma Jane
If your businesses considering an iPad point-of-sale (POS) system, you may be up for a challenge. Not only can the plethora of providers be overwhelming, but you must also remember that not all iPad POS systems are created equal. iPad POS systems do more than process payments and complete transactions. They also offer advanced capabilities that streamline operations. For instance, they can eliminate manual data entry by integrating accounting software, customer databases and inventory counts in real time, as each transaction occurs. With these systems, you get 24/7 access to sales data without having to be in the store. The challenge, however, is knowing which provider and set of features offer the best iPad POS solution for your business. iPad POS systems vary in functionality far more than the traditional POS solutions and are often targeted at specific verticals rather than the entire market. For that reason, it’s especially important to compare features between systems to ultimately select the right system for your business.
To help you choose a provider, here are things to look for in an iPad POS system.
Backend capabilities
One of the biggest benefits of an iPad POS system is that it offers advanced features that can streamline your entire operations. These include backend processes, such as inventory tracking, data analysis and reporting, and social media integration. As a small business, two of the most important time saving and productivity-boosting features to look for are customer relationship management (CRM) capabilities and connectivity to other sales channels. You’ll want an iPad POS that has robust CRM and a customizable customer loyalty program. It should tell you which products are most and least frequently purchased by specific customers at various store locations. It should also be able to identify the frequent VIP shoppers from the less frequent ones at any one of your store locations, creating the ultimate customer loyalty program for the small business owner. If you own an online store or use a mobile app to sell your products and services, your iPad POS software should also be able to integrate those online platforms with in-store sales. Not only will this provide an automated, centralized sales database, but it can also help increase total sales. You should be able to sell effortlessly through online, mobile and in-store channels. Why should your customers be limited to the people who walk by your store? Your iPad POS should be able to help you sell your products through more channels, online and on mobile. E-commerce and mobile commerce (mCommerce) aren’t just for big box retailers.
Cloud-based
The functions of an iPad POS solution don’t necessarily have to stop in-store. If you want to have anytime, anywhere access to your POS system, you can use one of the many providers with advanced features that give business owners visibility over their stores, its records and backend processes using the cloud. The best tablet-based POS systems operate on a cloud and allow you to operate it from any location you want. An iPad POS provider, with a cloud-based iPad POS system, businesses can keep tabs on stores in real time using any device, as well as automatically back up data. This gives business owners access to the system on their desktops, tablets or smartphones, even when not inside their stores. Using a cloud-based system also protects all the data that’s stored in your point of sale so you don’t have to worry about losing your data or, even worse, getting it stolen. Because the cloud plays such a significant role, businesses should also look into the kind of cloud service an iPad POS provider uses. In other words, is the system a cloud solution capable of expanding, or is it an app on the iPad that is not dependent on the Internet? Who is the cloud vendor? Is it a premium vendor? The type of cloud a provider uses can give you an idea about its reliability and the functions the provider will offer.
Downtime and technical support
As a small business, you need an iPad POS provider that has your back when something goes wrong. There are two types of customer support to look for: Downtime support and technical support.
iPad POS systems are often cheaper and simpler than traditional systems, but that doesn’t mean you can ignore the product support needs. The POS is a key element of your business and any downtime will likely result in significant revenue loss. You could, for instance, experience costly downtime when you lose Internet connectivity. iPad POS systems primarily rely on the Web to perform their core functions, but this doesn’t mean that when the Internet goes down, your business has to go down, too. Many providers offer offline support to keep your business going, such as Always on Mode. The Always on Mode setting enables your business to continue running even in the event of an Internet outage. Otherwise, your business will lose money during a loss of connectivity. Downtime can also happen due to technical problems within the hardware or software. Most iPad POS providers boast of providing excellent tech support, but you never really know what type of customer service you’ll actually receive until a problem occurs.
Test the friendliness of customer service reps by calling or emailing the provider with questions and concerns before signing any contracts. This way, you can see how helpful their responses are before you purchase their solution. Your POS is the most important device in your store. It’s essentially the gateway to all your transactions, customer data and inventory. If anything happens to it, you’ll need to be comfortable knowing that someone is there to answer your questions and guide you through everything.
Grows with your business
All growing businesses need tech solutions that can grow right along with them. Not all iPad POS systems are scalable, so look for a provider that makes it easy to add on more terminals and employees as your business expands. Pay attention to how the software handles growth in sales and in personnel. As a business grows, so does it sales volume and the required software capabilities. Some iPad POS solutions are designed for very small businesses, offering very limited features and transactions. If you have plans for growth, look for a provider that can handle the changes in transactions your business will be going through. Find out about features and customization. Does the system do what you want it to do? Can it handle large volume? How much volume? What modules can you add, and how do you interface to third parties? You should also consider the impacts of physical expansion and adding on new equipment and employees. If there are plans in the future for you to open another store location, you’ll need to make sure that your point of sale has the capabilities of actually handling another store location without adding more work for you. If you plan on hiring more employees for your store, you’ll also want to know that the solution you choose can easily be learned, so onboarding new staff won’t take up too much of your time.
Security
POS cyber attacks have risen dramatically over the past couple of years, making it more critical than ever to protect your business. Otherwise, it’s not just your business information at risk, but also your reputation and entire operations. iPad POS system security is a bit tricky, however. Unlike credit card swipers and mobile credit card readers that have long-established security standards namely, Payment Card Industry (PCI) compliance — the criteria for the iPad hardware itself as a POS terminal aren’t quite so clear-cut. Since iPads cannot be certified as PCI compliant, merchants must utilize a point-to-point encryption system that leaves the iPad out of scope. This means treating the iPad as its own system, which includes making sure it doesn’t save credit-card information or sensitive data on the iPad itself. To stay protected, look for PCI-certified, encrypted card swipers.
Posted in Best Practices for Merchants, Mobile Point of Sale, Point of Sale Tagged with: (POS) systems, accounting, app, business, card, cloud-based, credit, credit card readers, credit-card, crm, customer, customer relationship management, customer support, data, data analysis, database, desktops, e-commerce, inventory, iPad Point-Of-Sale, loyalty program, mcommerce, mobile, mobile app, mobile commerce, online, online platforms, Payment Card Industry, payments, PCI, platforms, POS, POS solution, products, sales, Security, security standards, services, Smartphones, social media, software, tablets, terminal, transactions, web
September 4th, 2014 by Elma Jane
EMV, which stands for Europay, MasterCard and Visa, and is slated to be mandated across the United States starting in October 2015 and automated fuel dispensers have until October 2017 to comply. Unlike magnetic swipe cards, EMV chip cards encrypt data and authenticate communication between the card and card reader. Additionally, chip card user is prompted for a PIN for authentication.
Why are those dates important? Companies lose $5.33 billion to fraud today, with card issuers and merchants incurring 63 and 37 percent of these losses, respectively. Under the EMV mandate, merchants who do not process chip cards will bear the burden of the issuer loss. By accepting chip card transactions, merchants and issuers should see a reduction in fraud.
Overcoming Barriers to EMV Adoption
Given the significant barriers to EMV adoption, it may be tempting for merchants to meet minimum requirements for accepting EMV payments. However, medium to large retailers should also consider the bigger picture of customer security and peace of mind.
Some key critical success factors for a payment initiative of this size include:
Business Continuity Architecture: As with all payment systems, it is imperative to have the EMV system running at all times. The solution should preferably have Active-Active architecture across multiple data centers and have a low Recovery Point Objective (the point in time to which the systems and data must be recovered after an outage).
Cost Benefit Analysis: Take a top down approach and decide accordingly on the scope of the analysis. This will ensure that decisions on scope are made on basis of quantitative data and not just qualitative arguments.
Phased Approach: To overcome time or cost overage in a project of this scope and complexity, retailers should try using an iterative approach for development. The rollout can be divided into multiple releases of six to seven months, which will provide the opportunity to review, capture lessons learnt, and improve subsequent releases.
Proactive Monitoring Alerts: Considering the criticality of business function carried out by EMV, tokenization and payment gateway, a vigorous supervising environment must be defined to perform proactive and reactive monitoring. It should take into consideration the monitoring targets, tools, scope and methods. This will provide advance visibility to the failure points and better ensuring maximum system availability.
Resilience Testing: Typically in a software project, the testing is limited to the unit, integration, performance and user acceptance. However, due to the critical nature of the applications and systems involved, robust resiliency testing is vital. This will ensure that there are no single points of failure and the system remains available when running in error conditions.
Stakeholder Identification: This is a key step to ensure that you have varied perspectives from all departments and their support. It will keep your organization from being blindsided and reduce the risk of disagreements in later stages of the program. Key stakeholders should include Store Operations, Card Accounting, Loss Prevention, Contact Center and IT & Data Security.
Organizations should adopt a five step approach to implement a secure, robust and industry-leading payment solution:
Encryption – Point to point encryption will ensure card data is secure and encrypted from the point of capture to the processor. Usually, merchants use data encryption that is not point to point, rendering their organization vulnerable to data breaches. Software encryption is the most common form of encryption, as it is easily installed and quires little or no hardware upgrades; however, it is less secure, may expose encryption keys, and is prone to memory scanning attacks. Hardware encryption is considered more secure but requires more costly terminal upgrades. Hardware encryption is designed to self-destruct the keys if tampered, but is not well-defined as very limited headway has been made in this space.
Tokenization – Build a Card Data Environment (CDE) that will host a centralized card data storage solution. Only limited applications with firewall access and capability to mutually authenticate via certificates can access CDE and receive card data. The rest of the applications will have tokens which are random numbers. This architecture will ease the merchant’s burden with existing and emerging PCI Data Security Standards.
Payment Gateway – Perform a risk assessment on the current payment gateway and identify gaps in functionality, manageability, compliance, scalability, speed to market and best practices. Determine the alternatives to mitigate the risks. Some of the important aspects of a leading payment gateway solution are support for all forms of credit, debit, gift cards and check transactions. Its ability to work with any acquirer, in-built encryption abilities, support for settlement and reconciliation must also be kept into consideration.
Settlement, Funding and Reconciliation – A workflow-based system to handle chargebacks and the automation of chargeback processing will greatly reduce labor-intensive work and enhance the quality of data used for settlement and reconciliation. Upgrades to the existing receipt retrieval system may be needed.
Card fraud is on the rise in the U.S., and merchants are the primary target for stealing information. With the EMV deadline just over a year away, the responsible retailer must take steps to prepare now. Although EMV implementation might seem overwhelming to merchants, they should start their journey to secure payments rather than wait for a looming deadline. Solutions such as data encryption and tokenization should be used in combination with EMV to implement a robust payment solution to better protect merchants against fraud. By proactively adopting EMV payment solutions, merchants can stay ahead of the regulatory curve and better protect their customers from fraud.
Posted in Best Practices for Merchants, Credit Card Security, EMV EuroPay MasterCard Visa, Payment Card Industry PCI Security, Visa MasterCard American Express Tagged with: authentication, automation, card, card data, Card Data Environment, card fraud, card issuers, card transactions, CDE, chargeback, chargeback processing, check, check transactions, chip, chip cards, credit, customer, customer security, data, data breaches, data encryption, data security, debit, EMV, emv chip cards, EuroPay, fraud, gateway, Gift Cards, host, integration, magnetic swipe cards, MasterCard, Merchant's, payment, payment gateway, payment solution, payment systems, PCI, PCI Data Security Standards, PIN, processor, retailers, Security, software, swipe, terminal, tokenization, tools, visa
September 2nd, 2014 by Elma Jane
While Apple doesn’t talk about future products,latest report that the next iPhone would include mobile-payment capabilities powered by a short-distance wireless technology called near-field communication or NFC. Apple is hosting an event on September 9th, that’s widely expected to be the debut of the next iPhone or iPhones. Mobile payments, or the notion that you can pay for goods and services at the checkout with your smartphone, may finally break into the mainstream if Apple and the iPhone 6 get involved.
Apple’s embrace of mobile payments would represent a watershed moment for how people pay at drugstores, supermarkets or for cabs. The technology and capability to pay with a tap of your mobile device has been around for years, you can tap an NFC-enabled Samsung Galaxy S5 or NFC-enabled credit card at point-of-sale terminals found at many Walgreen drugstores, but awareness and usage remain low. Apple has again the opportunity to transform, disrupt and reshape an entire business sector. It is hard to overestimate what impact Apple could have if it really wants to play in the payments market.
Apple won’t be the first to enter the mobile-payments arena. Google introduced its Google Wallet service in May 2011. The wireless carriers formed their joint venture with the intent to create a platform for mobile payments. Apple tends to stay away from new technologies until it has had a chance to smooth out the kinks. It was two years behind some smartphones in offering an iPhone that could tap into the faster LTE wireless network. NFC was rumored to be included in at least the last two iPhones and could finally make its appearance in the iPhone 6. The technology will be the linchpin to enabling transactions at the checkout.
Struggles
The notion of turning smartphones into true digital wallets including the ability to pay at the register, has been hyped up for years. But so far, it’s been more promise than results. There have been many technical hurdles to making mobile devices an alternative to cash, checks, and credit cards. NFC technology has to be included in both the smartphone and the point-of-sale terminal to work, and it’s been a slow process getting NFC chips into more equipment. NFC has largely been relegated to a feature found on higher-end smartphones such as the Galaxy S5 or the Nexus 5. There’s also confusion on both sides, the merchant and the customer, on how the tech works and why tapping your smartphone on a checkout machine is any faster, better or easier than swiping a card. There’s a chicken-and-egg problem between lack of user adoption and lack of retailer adoption. It’s one reason why even powerhouses such as Google have struggled. Despite a splashy launch of its digital wallet and payment service more than three years ago, Google hasn’t won mainstream acceptance or even awareness for its mobile wallet. Google hasn’t said how many people are using Google Wallet, but a look at its page on the Google Play store lists more than 47,000 reviews giving it an average of a four-star rating.
The Puzzle
Apple has quietly built the foundation to its mobile-payment service in Passbook, an app introduced two years ago in its iOS software and released as a feature with the iPhone 4S. Passbook has so far served as a repository for airline tickets, membership cards, and credit card statements. While it started out with just a handful of compatible apps, Passbook works with apps from Delta, Starbucks, Fandango, The Home Depot, and more. But it could potentially be more powerful. Apple’s already made great inroads with Passbook, it could totally crack open the mobile payments space in the US. Apple could make up a fifth of the share of the mobile-payment transactions in a short few months after the launch. The company also has the credit or debit card information for virtually all of its customers thanks to its iTunes service, so it doesn’t have to go the extra step of asking people to sign up for a new service. That takes away one of the biggest hurdles to adoption. The last piece of the mobile-payments puzzle with the iPhone is the fingerprint recognition sensor Apple added into last year’s iPhone 5S. That sensor will almost certainly make its way to the upcoming iPhone 6. The fingerprint sensor, which Apple obtained through its acquisition of Authentic in 2012, could serve as a quick and secure way of verifying purchases, not just through online purchases, but large transactions made at big-box retailers such as Best Buy. Today, you can use the fingerprint sensor to quickly buy content from Apple’s iTunes, App and iBooks stores.
The bigger win for Apple is the services and features it could add on to a simple transaction, if it’s successful in raising the awareness of a form of payment that has been quietly lingering for years. Google had previously seen mobile payments as the optimal location for targeted advertisements and offers. It’s those services and features that ultimately matter in the end, replacing a simple credit card swipe isn’t that big of a deal.
Posted in Best Practices for Merchants, Mobile Payments, Mobile Point of Sale, Smartphone Tagged with: app, Apple, card, card swipe, cash, checkout machine, checks, chips, credit, credit card swipe, credit-card, customer, debit card, Digital wallets, fingerprint recognition, fingerprint sensor, Galaxy S5, Google Wallet, iOS, Iphone, market, merchant, mobile, mobile device, mobile payment, mobile wallet, Near Field Communication, network, Nexus 5, nfc, payment, payment service, platform, point of sale, products, sensor, services, smartphone, software, statements, swiping card, terminals, transactions, wireless technology
August 28th, 2014 by Elma Jane
Merchants are still using pedestrian passwords that crooks can easily break, security company Trustwave has found. Of the nearly 630,000 stored passwords that Trustwave obtained during penetration tests in the past two years, its technicians were able to crack more than half in just a few minutes and 92% within 31 days. Even though adding new information about weak passwords or ongoing malware investigations gets frustrating because the same problems facing the financial and payments industries persist, it does not surprise Trustwave researchers. For a lot of software or hardware developers, their main concern is availability of the service. They want to make sure their POS is available and running to accept credit cards, often at the cost of a lot of security controls. It is difficult to implement security and to do it correctly.
Trustwave recommends longer passwords with more characters, rather than shorter ones with letters and numbers. A longer password that is a phrase not easily figured out is better than a shorter, complex password. These findings have been added to an online version of the 2014 Trustwave Global Security Report. To accommodate the fast changing nature of security threats, Trustwave is regularly updating its research and making the information available to consumers and payments industry stakeholders on the company’s site. The criminals stealing data are a constantly moving target. It no longer made sense for those interested in our research to have to wait a year to see new statistics. Having access to updated security reporting should be helpful to merchants. They can see how trends are tracking over time, instead of constantly having to go online to see what is relevant to them or rely on the trade groups to keep them informed. This provides one switch to keep them in the know, so there is some value there and it’s a smart move on Trustwave’s part. Since the new Payment Card Industry security requirements call for security measures to be embedded in software development lifecycles, there is some utility in Trustwave’s new approach to sharing research information.
Trustwave said the trend of businesses detecting breaches continues to rise, with 29% of businesses doing so in 2013 compared to only 9% in 2009. Trustwave compiled that data from 691 post-breach forensics investigations conducted in 2013. The report also indicated e-commerce breaches are increasing, with 54% of all breaches targeting e-commerce sites in 2013, compared to only 9% in 2010. More regions, including the U.S., being in various stages of converting to EMV chip-based cards for card-present transactions fuels the criminals’ shift to e-commerce fraud. Additionally, the company is working with law enforcement officials after discovering a control center of eight servers behind what is being called Magnitude, an exploit kit of Russian origin that has led to thousands of attacks and millions of attempted malware attacks globally.
Posted in Best Practices for Merchants, Payment Card Industry PCI Security, Point of Sale Tagged with: breaches, card, card-present transactions, company, credit cards, data, e-commerce, EMV chip-based cards, financial, fraud, Global Security, hardware, industry, Malware, Merchant's, online, passwords, payment, Payment Card Industry security, payments, payments industries, POS, Security, servers, software
August 27th, 2014 by Elma Jane
An IT services firm, announced earlier this week that it purchased a majority stake in cloud-based travel management company. With the move,hopes to strengthen its travel vertical by using software-as-a service travel IT platform. The future of software services lies in blending models with customized solutions and services over different stages of an enterprise lifecycle and across different business segments within the enterprise. The platform combined with the strong management team and travel domain specialist will further strengthen competitive position in the travel vertical.
Posted in Best Practices for Merchants, Travel Agency Agents Tagged with: business, cloud-based, company, domain, IT, management, platform, service, software, solutions, specialist, team, travel, travel domain, travel management, travel vertical
August 27th, 2014 by Elma Jane
Backoff malware that has attacked point of sale systems at hundreds of businesses may accelerate adoption of EMV chip and PIN cards and two-factor authentication as merchants look for ways to soften the next attack. Chip and PIN are a big thing, because it greatly diminishes the value of the information that can be trapped by this malware, said Trustwave, a security company that estimates about 600 businesses have been victims of the new malware. The malware uses infected websites to infiltrate the computing devices that host point of sale systems or are used to make payments, such as PCs, tablets and smartphones. Merchants can install software that monitors their payments systems for intrusions, but the thing is you can’t just have anti-virus programs and think you are safe. Credit card data is particularly vulnerable because the malware can steal data directly from the magnetic stripe or keystrokes used to make card payments.
The point of sale system is low-hanging fruit because a lot of businesses don’t own their own POS system. They rent them, or a small business may hire a third party to implement their own point of sale system. The Payment Card Industry Security Standards Council issued new guidance this month to address security for outsourced digital payments. EMV-chip cards, which are designed to deter counterfeiting, would gut the value of any stolen data. With this magnetic stripe data, the crooks can clone the card and sell it on the black market. With chip and PIN, the data changes for each transaction, so each transaction is unique. Even if the malware grabs the data, there not a lot the crooks can do with it. The EMV transition in the U.S. has recently accelerated, driven in part by recent highprofile data breaches. Even with that momentum, the U.S. may still take longer than the card networks’ October 2015 deadline to fully shift to chip-card acceptance.
EMV does not by itself mitigate the threat of breaches. Two-factor authentication, or the use of a second channel or computing device to authorize a transaction, will likely share in the boost in investment stemming from data security concerns. The continued compromise of point of sale merchants through a variety of vectors, including malware such as Backoff, will motivate the implementation among merchants of stronger authentication to prevent unauthorized access to card data.
Backoff has garnered a lot of attention, including a warning from the U.S. government, but it’s not the only malware targeting payment card data. It is not the types of threats which are new, but rather the frequency with which they are occurring which has put merchants on their heels. There is also an acute need to educate small merchants on both the threats and respective mitigation techniques.. The heightened alert over data vulnerability should boost the card networks’ plans to replace account numbers with substitute tokens to protect digital payments. Tokens would not necessarily stop crooks from infiltrating point of sale systems, but like EMV technology, they would limit the value of the stolen data. There are two sides to the equation, the issuers and the merchants. To the extent we see both sides adopt tokenization, you will see fewer breaches and they will be less severe because the crooks will be getting a token instead of card data.
Posted in Best Practices for Merchants, Credit Card Security, Payment Card Industry PCI Security, Point of Sale Tagged with: access, account, account numbers, anti-virus programs, authentication, Backoff, card, card networks, chip, credit, Credit card data, credit-card, data, data breaches, devices, digital payments, EMV, magnetic stripe, Malware, Merchant's, Payment Card Industry, payments, PCs, PIN, PIN cards, point of sale, POS, POS system, programs, Security, security standards, Smartphones, software, system, tablets, tokenization, tokens, transaction, Trustwave, websites